File Info
| Exam | Aruba Certified Clearpass Professional v6.2 |
| Number | ACCP-v6.2 |
| File Name | Aruba.ACCP-v6.2.Train4Sure.2018-06-24.83q.vcex |
| Size | 9 MB |
| Posted | Jun 24, 2018 |
| Download | Aruba.ACCP-v6.2.Train4Sure.2018-06-24.83q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
What database in the Policy Manager contains the device attributes derived by profiling?
- Local Users Repository
- Onboard Devices Repository
- Endpoints Repository
- Guest User Repository
- Client Repository
Correct answer: C
Question 2
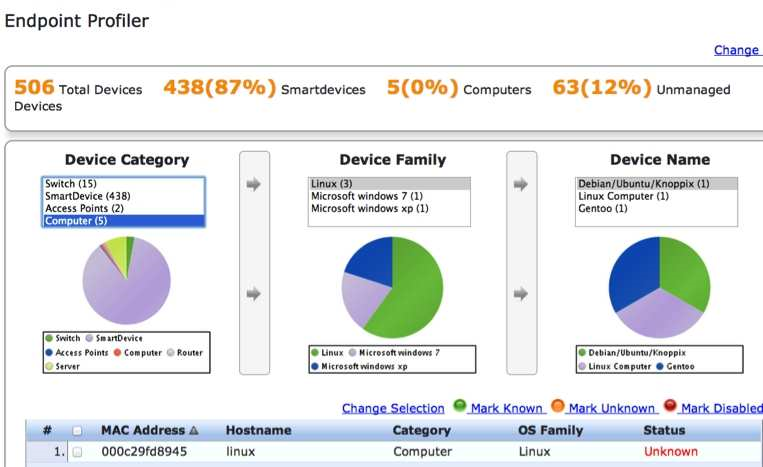
Refer to the screen capture below:
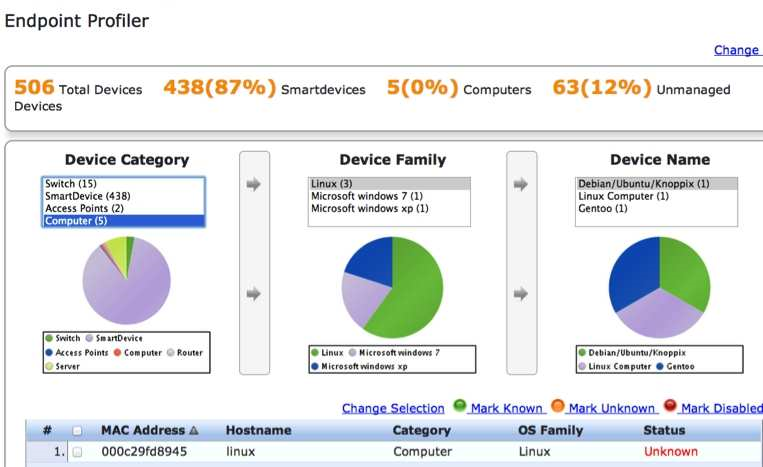
Based on the Endpoint Profiler output shown here, which of the following statements is true?
- The devices have been profiled using DHCP fingerprinting.
- There are 5 devices profiled in the Computer Device Category.
- Apple devices will be profiled in the SmartDevice category.
- There is only 1 Microsoft Windows device present in the network.
- The linux device with MAC address 000c29fd8945 has not been profiled.
Correct answer: B
Explanation:
Question 3
Which of the following conditions can be used for rule creation of an Enforcement Policy? (Choose 3)
- System Time
- Clearpass IP address
- Posture
- Switch VLAN
- Connection Protocol
Correct answer: ACE
Question 4
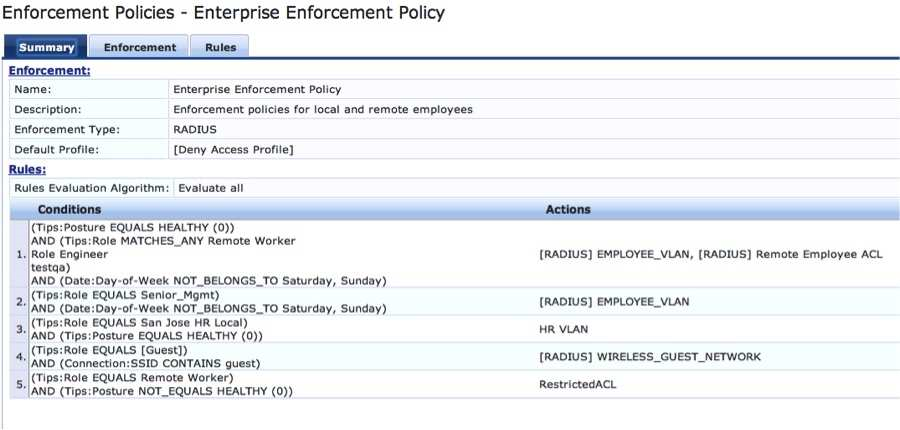
Refer to the screen capture below:
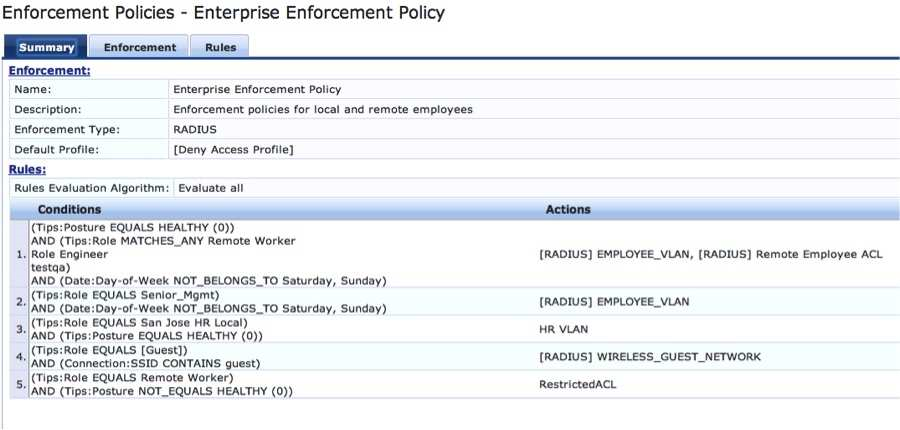
Based on the Enforcement Policy configuration, if a user with Role Engineer connects to the network and the posture token assigned is Unknown, what
Enforcement Profile will be applied?
- EMPLOYEE_VLAN
- Remote Employee ACL
- RestrictedACL
- Deny Access Profile
- HR VLAN
Correct answer: D
Question 5
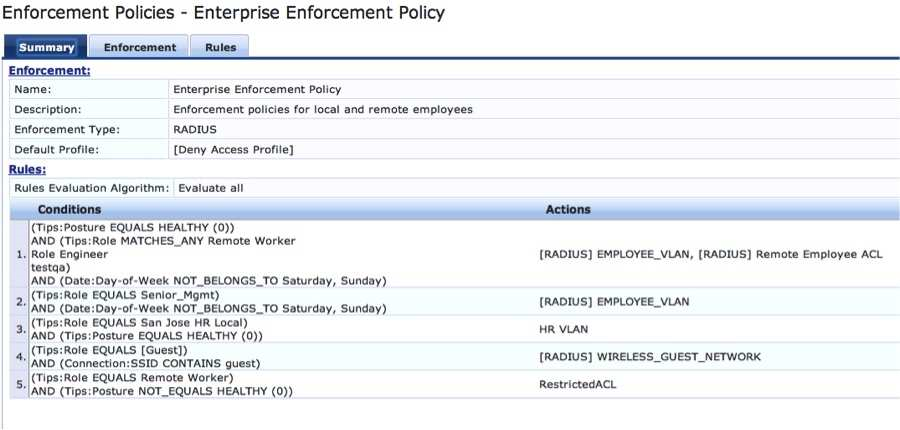
Refer to the screen capture below:
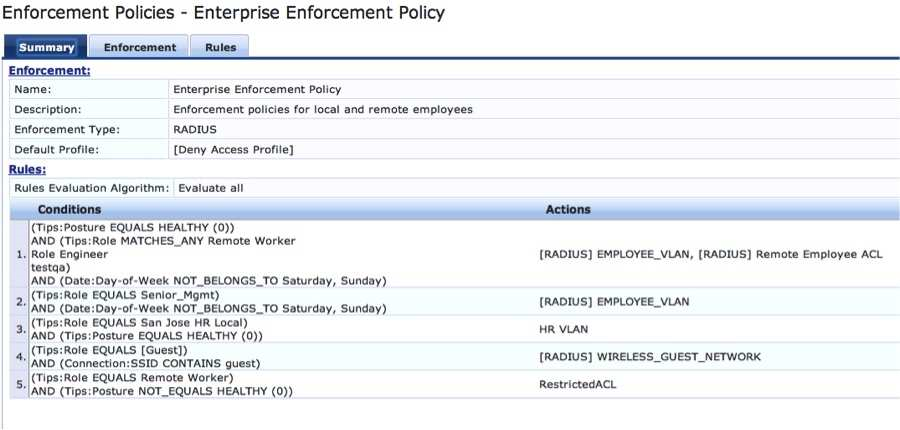
Based on the Enforcement Policy configuration, if a user with Role Remote Worker connects to the network and the posture token assigned is quarantine, what
Enforcement Profile will be applied?
- EMPLOYEE_VLAN
- Remote Employee ACL
- RestrictedACL
- Deny Access Profile
- HR VLAN
Correct answer: C
Question 6
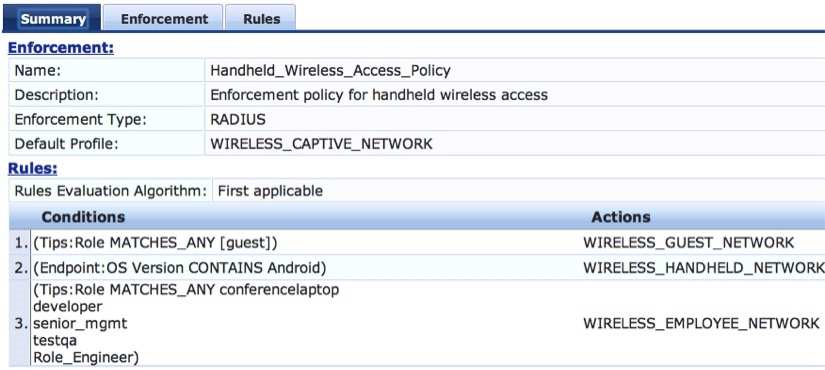
Refer to the screen capture below:
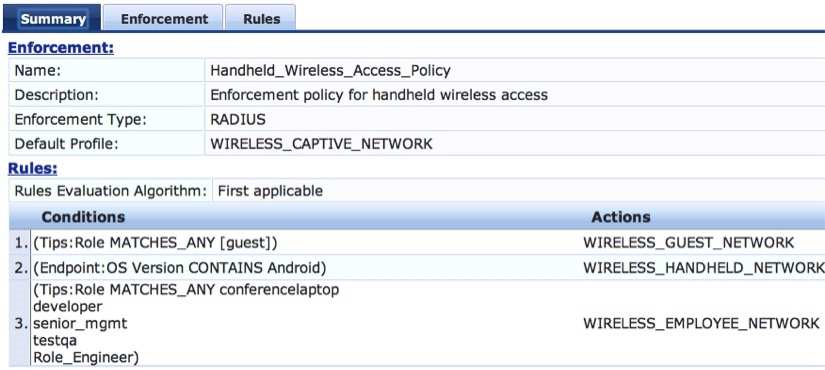
Based on the Enforcement Policy configuration, if a user connects to the network using an Apple iphone, what Enforcement Profile is applied?
- WIRELESS_CAPTIVE_NETWORK
- WIRELESS_HANDHELD_NETWORK
- WIRELESS_GUEST_NETWORK
- WIRELESS_EMPLOYEE_NETWORK
- Deny Access
Correct answer: A
Question 7
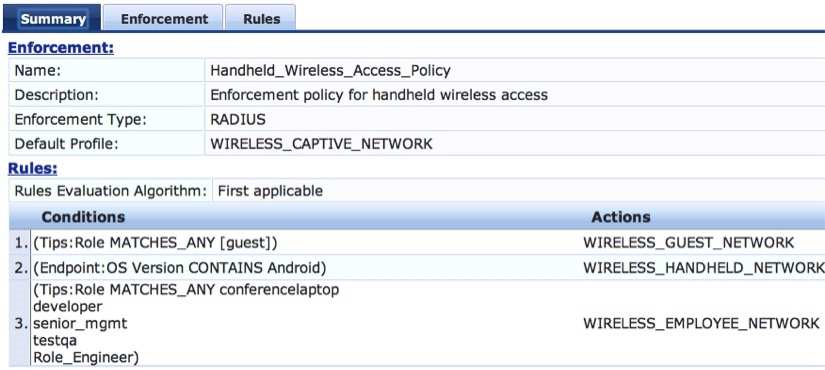
Refer to the screen capture below:
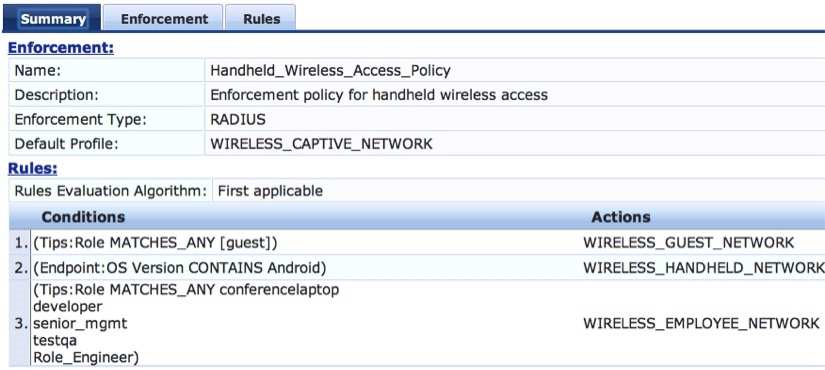
A user who is tagged with the ClearPass roles of Role_Engineer and developer, but not testqa, connects to the network with a corporate Windows laptop.
What Enforcement Profile is applied?
- WIRELESS_CAPTIVE_NETWORK
- WIRELESS_HANDHELD_NETWORK
- WIRELESS_GUEST_NETWORK
- WIRELESS_EMPLOYEE_NETWORK
- Deny Access
Correct answer: D
Question 8
Which of the following components of a Policy Service is mandatory?
- Enforcement
- Posture
- Profiler
- Role Mapping Policy
- Authorization Source
Correct answer: A
Question 9
Which of the following options is the correct order of steps of a Policy Service request?
1) Clearpass tests the request against Service Rules to select a Policy Service.
2) Clearpass applies the Enforcement Policy.
3) Negotiation of the Authentication Method occurs between the NAD and Clearpass.
4) Clearpass sends the Enforcement Profile attributes to the NAD.
5) NAD forwards authentication request to Clearpass.
- 1, 3, 2, 4, 5
- 5, 1, 3, 2, 4
- 5, 1, 3, 4, 2
- 1, 2, 3, 4, 5
- 2, 3, 4, 5, 1
Correct answer: B
Question 10
Which of the following information is NOT required while building a Policy Service for 802.1X authentication?
- Network Access Device used
- Authentication Method used
- Authentication Source used
- Posture Token of the client
- Profiling information of the client
Correct answer: D

