File Info
| Exam | BTA Certified Blockchain Solution Architect |
| Number | CBSA |
| File Name | Blockchain.CBSA.Pass4Sure.2019-10-21.119q.vcex |
| Size | 370 KB |
| Posted | Oct 21, 2019 |
| Download | Blockchain.CBSA.Pass4Sure.2019-10-21.119q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
Secure Hash Algorithm (SHA-256) output is always 256 bits or 32 bytes in length regardless of the length of the input (even if input is millions of bytes). Select best answer.
- NSA is spying on us so what’s it matters.
- Depends on input
- False
- True
Correct answer: D
Explanation:
SHA stands for Secure Hash Algorithm. This is used to prove data integrity. The same input(s) will always produce the exact same output. This output is always 256 bits or 32 bytes in length regardless of the length of the input (even if input is millions of bytes). Reference: https://medium.com/all-things-ledger/bitcoins-implementation-of-blockchain-2be713f662c2 SHA stands for Secure Hash Algorithm. This is used to prove data integrity. The same input(s) will always produce the exact same output. This output is always 256 bits or 32 bytes in length regardless of the length of the input (even if input is millions of bytes).
Reference: https://medium.com/all-things-ledger/bitcoins-implementation-of-blockchain-2be713f662c2
Question 2
In the Ethereum EVM there are two types of memory areas. (Select two.)
- Storage
- Database
- Memory
- Persistent
- Ephemeral
Correct answer: AC
Explanation:
Reference: https://solidity.readthedocs.io/en/latest/introduction-to-smart-contracts.html#the-ethereum-virtual-machine Reference: https://solidity.readthedocs.io/en/latest/introduction-to-smart-contracts.html#the-ethereum-virtual-machine
Question 3
What are some advantages of Proof of Stake(POS) mining over Proof of Work(POW) mining? (Select three.)
- Energy efficient in regards to that it could consume for electricity as compared to PoW
- Faster Hashing algorithms
- No need for expensive compared to POW
- Faster validations compared to POW
- Better blockchain security compared to POW
Correct answer: ACD
Explanation:
This eliminates the below challenges from PoW and believed to have an advantage. No need of expensive hardware (a normal laptop or computer running the respective coin’s Validator client will do as long as your laptop or computer is online) Energy efficient as it won’t consume high electricity as PoW does More loyal Validators As higher the stake the Validators have for a long time, more chances for the Validator to be picked up for “forging” and earn the transaction fee Faster validations Reference: https://medium.com/@karthik.seshu/cryptocurrency-proof-of-work-vs-proof-of-stake-e1eee1420b10 This eliminates the below challenges from PoW and believed to have an advantage.
No need of expensive hardware (a normal laptop or computer running the respective coin’s Validator client will do as long as your laptop or computer is online)
Energy efficient as it won’t consume high electricity as PoW does More loyal Validators As higher the stake the Validators have for a long time, more chances for the Validator to be picked up for “forging” and earn the transaction fee Faster validations
Reference: https://medium.com/@karthik.seshu/cryptocurrency-proof-of-work-vs-proof-of-stake-e1eee1420b10
Question 4
Application Specific Integrated Circuit (ASIC) are used always in enterprise blockchains.
- TRUE
- FALSE
Correct answer: B
Explanation:
ASICS are generally used in blockchains such as BTC that have a Proof of Work consensus due to competition Reference: https://www.trymining.com/pages/asic-vs-gpu ASICS are generally used in blockchains such as BTC that have a Proof of Work consensus due to competition
Reference: https://www.trymining.com/pages/asic-vs-gpu
Question 5
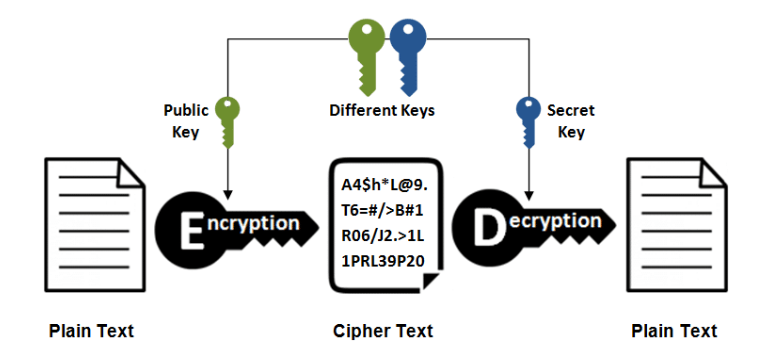
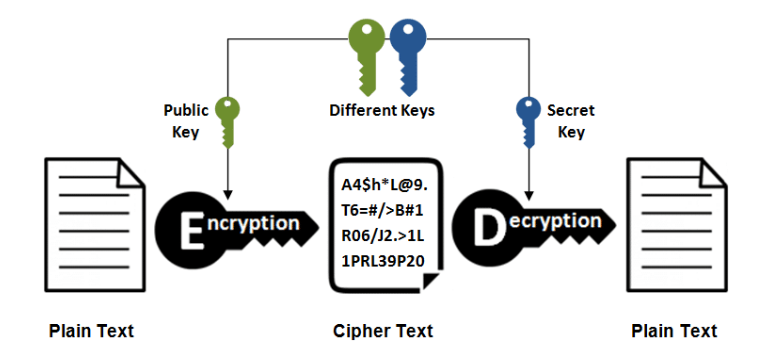
What type of encryption is shown below and is commonly used in blockchain cryptography?
- Diffie-Hellman
- Asymmetric Encryption
- Synchronous
- Asynchronous
- Symmetric Encryption
Correct answer: B
Explanation:
Asymmetric cryptography utilizes two different keys, a public key and a private to encrypt and decrypt a particular data. The use of one key cancels out the use of the other. Reference: https://blockgeeks.com/guides/cryptocurrencies-cryptography/ Asymmetric cryptography utilizes two different keys, a public key and a private to encrypt and decrypt a particular data. The use of one key cancels out the use of the other.
Reference: https://blockgeeks.com/guides/cryptocurrencies-cryptography/
Question 6
An encryption algorithm transforms plain text into cipher text using a key?
- TRUE
- FALSE
Correct answer: A
Question 7
The gas price is a value set by the creator of the blockchain transaction? (Select best answer.)
- FALSE
- Its Negotiable
- TRUE
Correct answer: C
Explanation:
The gas price is a value set by the creator of the transaction, who has to pay gas_price * gas up front from the sending account. If some gas is left after the execution, it is refunded in the same way. If the gas is used up at any point (i.e. it is negative), an out-of-gas exception is triggered, which reverts all modifications made to the state in the current call frame. Reference: https://solidity.readthedocs.io/en/latest/introduction-to-smart-contracts.html#the-ethereum-virtual-machine The gas price is a value set by the creator of the transaction, who has to pay gas_price * gas up front from the sending account. If some gas is left after the execution, it is refunded in the same way. If the gas is used up at any point (i.e. it is negative), an out-of-gas exception is triggered, which reverts all modifications made to the state in the current call frame.
Reference: https://solidity.readthedocs.io/en/latest/introduction-to-smart-contracts.html#the-ethereum-virtual-machine
Question 8

R3 Corda does not organize time into blocks. What does Corda actually perform and use?

- Ripple is implemented as the blockchain and XRP for cryptocurrency.
- Notary services and timesmapping
- R3 Corda is a blockchain and does use blocks
- Notary services and timestamping
Correct answer: D
Explanation:
Review Technical Whitepaper https://www.corda.net/ Corda network has one or more notary services which provide transaction ordering and timestamping services, thus abstracting the role miners play in other systems into a pluggable component. Review Technical Whitepaper https://www.corda.net/ Corda network has one or more notary services which provide transaction ordering and timestamping services, thus abstracting the role miners play in other systems into a pluggable component.
Question 9
Contracts live on the blockchain in an Ethereum-specific binary format called _____________?
- EOS
- EVM Code
- Ether
- Gas
- EVM Bytecode
Correct answer: E
Explanation:
The Ethereum Virtual Machine (EVM) is the runtime environment for smart contracts in Ethereum. It is not only sandboxed, but actually completely isolated, which means that code running inside the EVM has no access to network, filesystem, or other processes. Smart contracts even have limited access to other smart contracts. The Ethereum Virtual Machine (EVM) is the runtime environment for smart contracts in Ethereum. It is not only sandboxed, but actually completely isolated, which means that code running inside the EVM has no access to network, filesystem, or other processes. Smart contracts even have limited access to other smart contracts.
Question 10
Bitcoin uses what proof of work consensus system?
- Cubehash512
- Scrypt-Jane
- Whirlpool
- Scrypt-n
- Hashcash
Correct answer: E
Explanation:
Bitcoin uses the Hashcash proof of work system. Reference: https://en.bitcoin.it/wiki/Hashcash Bitcoin uses the Hashcash proof of work system.
Reference: https://en.bitcoin.it/wiki/Hashcash

