File Info
| Exam | Check Point Certified Security Administrator |
| Number | 156-215.80 |
| File Name | Checkpoint.156-215.80.BrainDumps.2017-03-16.141q.vcex |
| Size | 8 MB |
| Posted | Mar 16, 2017 |
| Download | Checkpoint.156-215.80.BrainDumps.2017-03-16.141q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
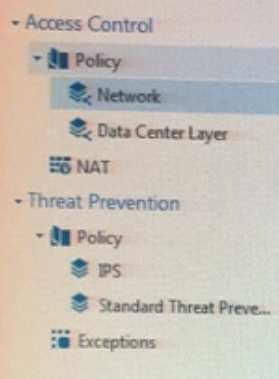
Review the following screenshot and select the BEST answer.
- Data Center Layer is an inline layer in the Access Control Policy.
- By default all layers are shared with all policies.
- If a connection is dropped in Network Layer, it will not be matched against the rules in Data Center Layer.
- If a connection is accepted in Network-layer, it will not be matched against the rules in Data Center Layer.
Correct answer: C
Question 2
Which of the following is NOT a SecureXL traffic flow?
- Medium Path
- Accelerated Path
- Fast Path
- Slow Path
Correct answer: C
Explanation:
SecureXL is an acceleration solution that maximizes performance of the Firewall and does not compromise security. When SecureXL is enabled on a Security Gateway, some CPU intensive operations are processed by virtualized software instead of the Firewall kernel. The Firewall can inspect and process connections more efficiently and accelerate throughput and connection rates. These are the SecureXL traffic flows:Slow path - Packets and connections that are inspected by the Firewall and are not processed by SecureXL. Accelerated path - Packets and connections that are offloaded to SecureXL and are not processed by the Firewall. Medium path - Packets that require deeper inspection cannot use the accelerated path. It is not necessary for the Firewall to inspect these packets, they can be offloaded and do not use the slow path. For example, packets that are inspected by IPS cannot use the accelerated path and can be offloaded to the IPS PSL (Passive Streaming Library). SecureXL processes these packets more quickly than packets on the slow path. Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Firewall_WebAdmin/92711.htm SecureXL is an acceleration solution that maximizes performance of the Firewall and does not compromise security. When SecureXL is enabled on a Security Gateway, some CPU intensive operations are processed by virtualized software instead of the Firewall kernel. The Firewall can inspect and process connections more efficiently and accelerate throughput and connection rates. These are the SecureXL traffic flows:
Slow path - Packets and connections that are inspected by the Firewall and are not processed by SecureXL.
Accelerated path - Packets and connections that are offloaded to SecureXL and are not processed by the Firewall.
Medium path - Packets that require deeper inspection cannot use the accelerated path. It is not necessary for the Firewall to inspect these packets, they can be offloaded and do not use the slow path. For example, packets that are inspected by IPS cannot use the accelerated path and can be offloaded to the IPS PSL (Passive Streaming Library). SecureXL processes these packets more quickly than packets on the slow path.
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Firewall_WebAdmin/92711.htm
Question 3
Which of the following Automatically Generated Rules NAT rules have the lowest implementation priority?
- Machine Hide NAT
- Address Range Hide NAT
- Network Hide NAT
- Machine Static NAT
Correct answer: BC
Explanation:
SmartDashboard organizes the automatic NAT rules in this order: Static NAT rules for Firewall, or node (computer or server) objects Hide NAT rules for Firewall, or node objects Static NAT rules for network or address range objects Hide NAT rules for network or address range objects Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_Firewall_WebAdmin/6724.htm SmartDashboard organizes the automatic NAT rules in this order:
- Static NAT rules for Firewall, or node (computer or server) objects
- Hide NAT rules for Firewall, or node objects
- Static NAT rules for network or address range objects
- Hide NAT rules for network or address range objects
Reference:
https://sc1.checkpoint.com/documents/R77/CP_R77_Firewall_WebAdmin/6724.htm
Question 4
Fill in the blanks: VPN gateways authenticate using ___________ and ___________ .
- Passwords; tokens
- Certificates; pre-shared secrets
- Certificates; passwords
- Tokens; pre-shared secrets
Correct answer: B
Explanation:
VPN gateways authenticate using Digital Certificates and Pre-shared secrets. Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_VPN_AdminGuide/85469.htm VPN gateways authenticate using Digital Certificates and Pre-shared secrets.
Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_VPN_AdminGuide/85469.htm
Question 5
In R80 spoofing is defined as a method of:
- Disguising an illegal IP address behind an authorized IP address through Port Address Translation.
- Hiding your firewall from unauthorized users.
- Detecting people using false or wrong authentication logins
- Making packets appear as if they come from an authorized IP address.
Correct answer: D
Explanation:
IP spoofing replaces the untrusted source IP address with a fake, trusted one, to hijack connections to your network. Attackers use IP spoofing to send malware and bots to your protected network, to execute DoS attacks, or to gain unauthorized access. Reference: http://dl3.checkpoint.com/paid/74/74d596decb6071a4ee642fbdaae7238f/CP_R80_SecurityManagement_AdminGuide.pdf?HashKey=1479584563_6f823c8ea1514609148aa4fec5425db2&xtn=.pdf IP spoofing replaces the untrusted source IP address with a fake, trusted one, to hijack connections to your network. Attackers use IP spoofing to send malware and bots to your protected network, to execute DoS attacks, or to gain unauthorized access.
Reference:
http://dl3.checkpoint.com/paid/74/74d596decb6071a4ee642fbdaae7238f/CP_R80_SecurityManagement_AdminGuide.pdf?HashKey=1479584563_6f823c8ea1514609148aa4fec5425db2&xtn=.pdf
Question 6
Fill in the blank: The __________ is used to obtain identification and security information about network users.
- User Directory
- User server
- UserCheck
- User index
Correct answer: A
Explanation:
Reference:https://www.checkpoint.com/downloads/product-related/datasheets/DS_UserDirectorySWB.pdf Reference:
https://www.checkpoint.com/downloads/product-related/datasheets/DS_UserDirectorySWB.pdf
Question 7
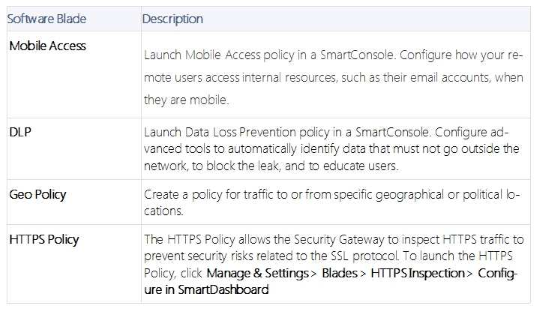
DLP and Geo Policy are examples of what type of Policy?
- Standard Policies
- Shared Policies
- Inspection Policies
- Unified Policies
Correct answer: B
Explanation:
The Shared policies are installed with the Access Control Policy. Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197 The Shared policies are installed with the Access Control Policy.
Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197
Question 8
In which deployment is the security management server and Security Gateway installed on the same appliance?
- Bridge Mode
- Remote
- Standalone
- Distributed
Correct answer: C
Explanation:
Installing Standalone Standalone Deployment - The Security Management Server and the Security Gateway are installed on the same computer or appliance. Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Installation_and_Upgrade_Guide-webAdmin/89230.htm#o98246 Installing Standalone
Standalone Deployment - The Security Management Server and the Security Gateway are installed on the same computer or appliance.
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Installation_and_Upgrade_Guide-webAdmin/89230.htm#o98246
Question 9
Fill in the blank: A _________ VPN deployment is used to provide remote users with secure access to internal corporate resources by authenticating the user through an internet browser.
- Clientless remote access
- Clientless direct access
- Client-based remote access
- Direct access
Correct answer: A
Explanation:
Clientless - Users connect through a web browser and use HTTPS connections. Clientless solutions usually supply access to web-based corporate resources. Reference: https://sc1.checkpoint.com/documents/R80/CP_R80BC_Firewall/html_frameset.htm?topic=documents/R80/CP_R80BC_Firewall/92704 Clientless - Users connect through a web browser and use HTTPS connections. Clientless solutions usually supply access to web-based corporate resources.
Reference: https://sc1.checkpoint.com/documents/R80/CP_R80BC_Firewall/html_frameset.htm?topic=documents/R80/CP_R80BC_Firewall/92704
Question 10
Which of the following statements is TRUE about R80 management plug-ins?
- The plug-in is a package installed on the Security Gateway.
- Installing a management plug-in requires a Snapshot, just like any upgrade process.
- A management plug-in interacts with a Security Management Server to provide new features and support for new products.
- Using a plug-in offers full central management only if special licensing is applied to specific features of the plug-in.
Correct answer: C

