File Info
| Exam | Check Point Certified Security Administrator |
| Number | 156-215.80 |
| File Name | Checkpoint.156-215.80.Test4Prep.2019-07-20.288q.vcex |
| Size | 7 MB |
| Posted | Jul 20, 2019 |
| Download | Checkpoint.156-215.80.Test4Prep.2019-07-20.288q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
Which of the following ClusterXL modes uses a non-unicast MAC address for the cluster IP address.
- High Availability
- Load Sharing Multicast
- Load Sharing Pivot
- Master/Backup
Correct answer: B
Explanation:
ClusterXL uses the Multicast mechanism to associate the virtual cluster IP addresses with all cluster members. By binding these IP addresses to a Multicast MAC address, it ensures that all packets sent to the cluster, acting as a gateway, will reach all members in the cluster. Reference:https://sc1.checkpoint.com/documents/R76/CP_R76_ClusterXL_AdminGuide/7292.htm ClusterXL uses the Multicast mechanism to associate the virtual cluster IP addresses with all cluster members. By binding these IP addresses to a Multicast MAC address, it ensures that all packets sent to the cluster, acting as a gateway, will reach all members in the cluster.
Reference:
https://sc1.checkpoint.com/documents/R76/CP_R76_ClusterXL_AdminGuide/7292.htm
Question 2
Fill in the blank: With the User Directory Software Blade, you can create R80 user definitions on a(an) ___________ Server.
- NT domain
- SMTP
- LDAP
- SecurID
Correct answer: C
Explanation:
Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197 Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197
Question 3
Which of the following is NOT a component of a Distinguished Name?
- Organization Unit
- Country
- Common name
- User container
Correct answer: D
Explanation:
Distinguished Name Components CN=common name, OU=organizational unit, O=organization, L=locality, ST=state or province, C=country name Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950 Distinguished Name Components
CN=common name, OU=organizational unit, O=organization, L=locality, ST=state or province, C=country name
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950
Question 4
What are the three authentication methods for SIC?
- Passwords, Users, and standards-based SSL for the creation of security channels
- Certificates, standards-based SSL for the creation of secure channels, and 3DES or AES128 for encryption
- Packet Filtering, certificates, and 3DES or AES128 for encryption
- Certificates, Passwords, and Tokens
Correct answer: B
Explanation:
Secure Internal Communication (SIC) Secure Internal Communication (SIC) lets Check Point platforms and products authenticate with each other. The SIC procedure creates a trusted status between gateways, management servers and other Check Point components. SIC is required to install polices on gateways and to send logs between gateways and management servers. These security measures make sure of the safety of SIC:Certificates for authentication Standards-based SSL for the creation of the secure channel 3DES for encryption Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950 Secure Internal Communication (SIC)
Secure Internal Communication (SIC) lets Check Point platforms and products authenticate with each other. The SIC procedure creates a trusted status between gateways, management servers and other Check Point components. SIC is required to install polices on gateways and to send logs between gateways and management servers.
These security measures make sure of the safety of SIC:
- Certificates for authentication
- Standards-based SSL for the creation of the secure channel
- 3DES for encryption
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950
Question 5
You have enabled “Full Log” as a tracking option to a security rule. However, you are still not seeing any data type information. What is the MOST likely reason?
- Logging has disk space issues. Change logging storage options on the logging server or Security Management Server properties and install database.
- Data Awareness is not enabled.
- Identity Awareness is not enabled.
- Logs are arriving from Pre-R80 gateways.
Correct answer: A
Explanation:
The most likely reason for the logs data to stop is the low disk space on the logging device, which can be the Management Server or the Gateway Server. The most likely reason for the logs data to stop is the low disk space on the logging device, which can be the Management Server or the Gateway Server.
Question 6
What is the order of NAT priorities?
- Static NAT, IP pool NAT, hide NAT
- IP pool NAT, static NAT, hide NAT
- Static NAT, automatic NAT, hide NAT
- Static NAT, hide NAT, IP pool NAT
Correct answer: A
Explanation:
The order of NAT priorities is:Static NAT IP Pool NAT Hide NAT Since Static NAT has all of the advantages of IP Pool NAT and more, it has a higher priority than the other NAT methods. Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_Firewall_WebAdmin/6724.htm#o6919 The order of NAT priorities is:
- Static NAT
- IP Pool NAT
- Hide NAT
Since Static NAT has all of the advantages of IP Pool NAT and more, it has a higher priority than the other NAT methods.
Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_Firewall_WebAdmin/6724.htm#o6919
Question 7
Which of the following is an identity acquisition method that allows a Security Gateway to identify Active Directory users and computers?
- UserCheck
- Active Directory Query
- Account Unit Query
- User Directory Query
Correct answer: B
Explanation:
AD Query extracts user and computer identity information from the Active Directory Security Event Logs. The system generates a Security Event log entry when a user or computer accesses a network resource. For example, this occurs when a user logs in, unlocks a screen, or accesses a network drive. Reference : https://sc1.checkpoint.com/documents/R76/CP_R76_IdentityAwareness_AdminGuide/62402.htm AD Query extracts user and computer identity information from the Active Directory Security Event Logs. The system generates a Security Event log entry when a user or computer accesses a network resource. For example, this occurs when a user logs in, unlocks a screen, or accesses a network drive.
Reference : https://sc1.checkpoint.com/documents/R76/CP_R76_IdentityAwareness_AdminGuide/62402.htm
Question 8
Ken wants to obtain a configuration lock from other administrator on R80 Security Management Server. He can do this via WebUI or a via CLI. Which command should be use in CLI? Choose the correct answer.
- remove database lock
- The database feature has one command lock database override.
- override database lock
- The database feature has two commands: lock database override and unlock database. Both will work.
Correct answer: D
Explanation:
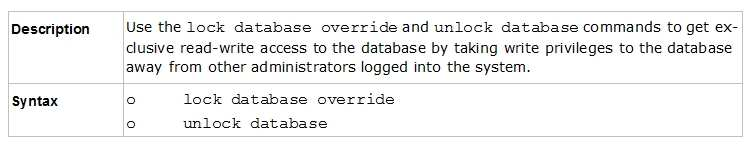
Use the database feature to obtain the configuration lock. The database feature has two commands:lock database [override]. unlock database The commands do the same thing: obtain the configuration lock from another administrator. Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Gaia_WebAdmin/75697.htm#o73091 Use the database feature to obtain the configuration lock. The database feature has two commands:
- lock database [override].
- unlock database
The commands do the same thing: obtain the configuration lock from another administrator.
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Gaia_WebAdmin/75697.htm#o73091
Question 9
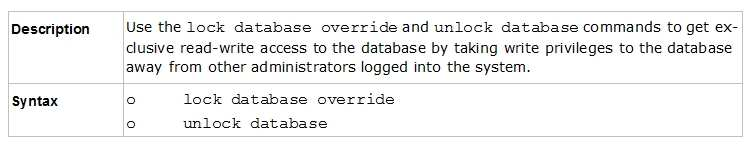
Examine the following Rule Base.
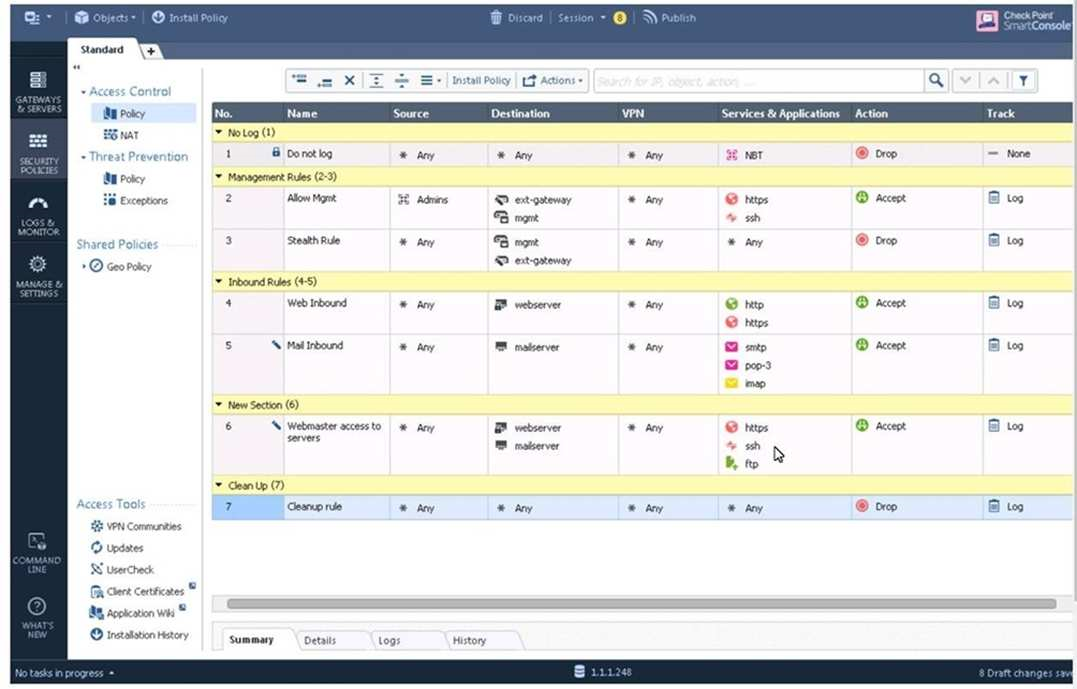
What can we infer about the recent changes made to the Rule Base?
- Rule 7 was created by the 'admin' administrator in the current session
- 8 changes have been made by administrators since the last policy installation
- Te rules 1, 5 and 6 cannot be edited by the 'admin' administrator
- Rule 1 and object webserver are locked by another administrator
Correct answer: D
Explanation:
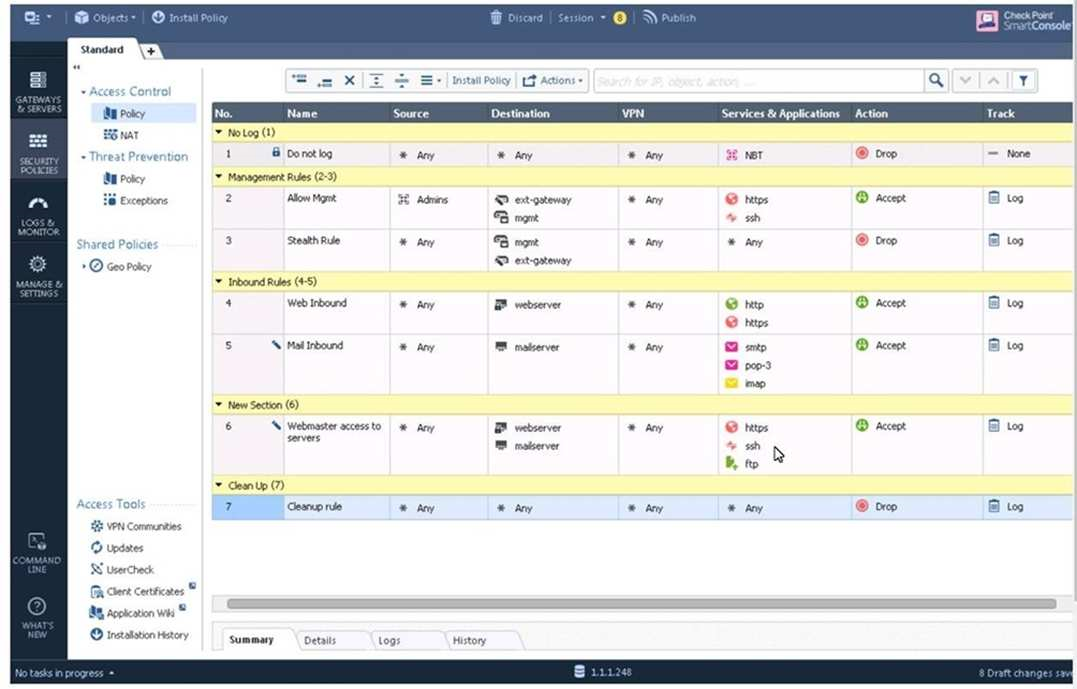
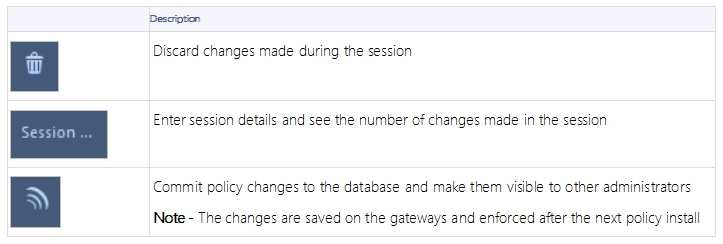
Explantation: On top of the print screen there is a number "8" which consists for the number of changes made and not saved. Session Management Toolbar (top of SmartConsole) Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/117948 Explantation:
On top of the print screen there is a number "8" which consists for the number of changes made and not saved.
Session Management Toolbar (top of SmartConsole)
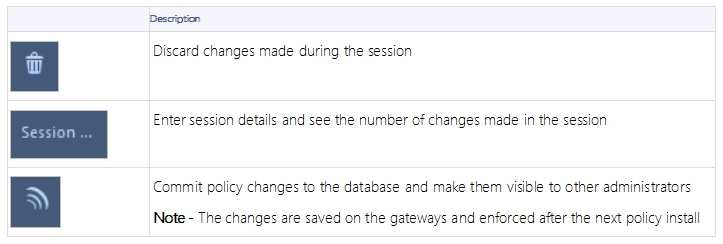
Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/117948
Question 10
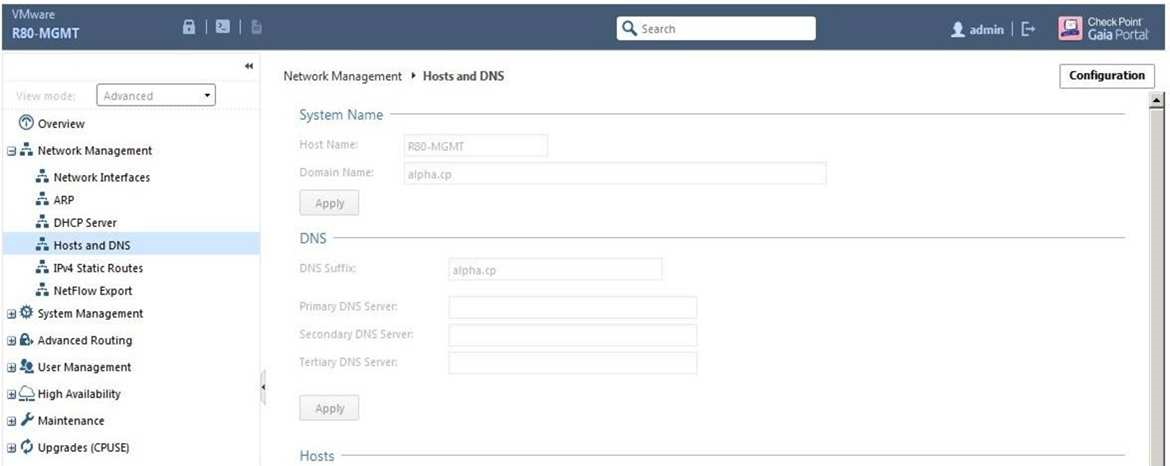
ALPHA Corp has a new administrator who logs into the Gaia Portal to make some changes. He realizes that even though he has logged in as an administrator, he is unable to make any changes because all configuration options are greyed out as shown in the screenshot image below. What is the likely cause for this?
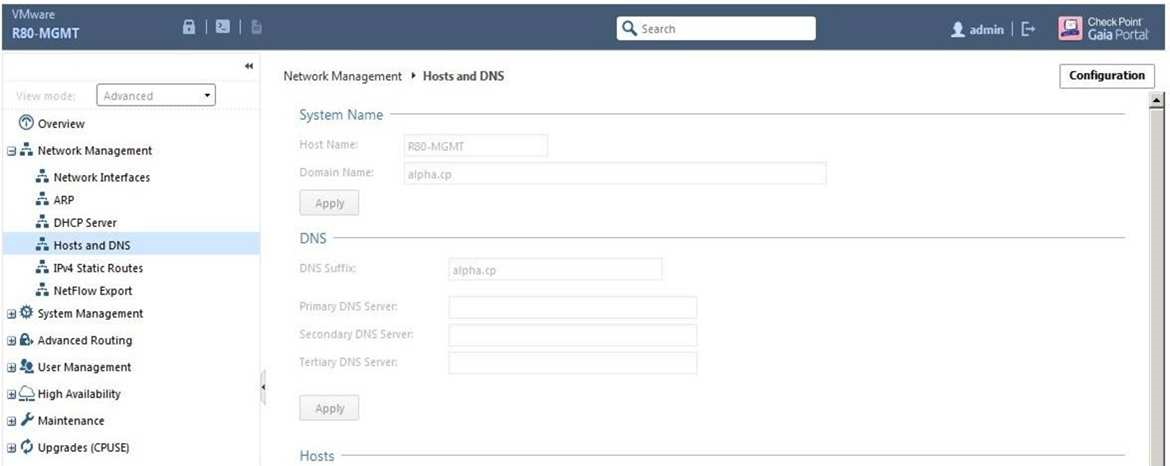
- The Gaia /bin/confd is locked by another administrator from a SmartConsole session.
- The database is locked by another administrator SSH session.
- The Network address of his computer is in the blocked hosts.
- The IP address of his computer is not in the allowed hosts.
Correct answer: B
Explanation:
There is a lock on top left side of the screen. B is the logical answer. There is a lock on top left side of the screen. B is the logical answer.

