File Info
| Exam | Cisco Certified Design Expert CCDE v3.0 |
| Number | 400-007 |
| File Name | Cisco.400-007.VCEplus.2022-11-16.30q.vcex |
| Size | 785 KB |
| Posted | Nov 16, 2022 |
| Download | Cisco.400-007.VCEplus.2022-11-16.30q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
An enterprise that runs numerous proprietary applications has major issues with its on-premises server estate hardware, to the point where business-critical functions are compromised. The enterprise accelerates plans to migrate services to the cloud. Which cloud service should be used if the enterprise wants to avoid hardware issues yet have control of its applications and operating system?
- SaaS
- PaaS
- laaS
- hybrid cloud
Correct answer: C
Explanation:
Question 2
Which two features control multicast traffic in a VLAN environment? (Choose two)
- IGMP snooping
- MLD snooping
- RGMP
- PIM snooping
- pruning
Correct answer: AB
Explanation:
Question 3
Company XYZ wants to secure the data plane of their network. Which two technologies can be included in the security design? (Choose two)
- DAI
- IP Source Guard
- BEEP
- CPPr
- MPP
Correct answer: AB
Explanation:
Question 4
Company XYZ has a new network based on IPv6. Some of the subnets that they are planning to use will be confidential and need an addressing scheme that confines them to the local campus network.
Which type of IPv6 addresses can be used for these networks in the IPv6 addressing design?
- local addresses
- private addresses
- link-local addresses
- unique local addresses
Correct answer: D
Explanation:
Question 5
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
- asynchronous replication over dual data centers via DWDM
- synchronous replication over geographically dispersed dual data centers via MPLS
- synchronous replication over dual data centers via Metro Ethernet
- asynchronous replication over geographically dispersed dual data centers via CWDM
Correct answer: C
Explanation:
Question 6
Which two data plane hardening techniques are true? (Choose two)
- warning banners
- redundant AAA servers
- Control Plane Policing
- infrastructure ACLs
- disable unused services
- routing protocol authentication
Correct answer: EF
Explanation:
Question 7
You have been asked to design a high-density wireless network for a university campus. Which two principles would you apply in order to maximize the wireless network capacity? (Choose two.)
- Implement a four-channel design on 2.4 GHz to increase the number of available channels
- Choose a high minimum data rate to reduce the duty cycle.
- increases the number of SSlDs to load-balance the client traffic.
- Make use of the 5-GHz band to reduce the spectrum utilization on 2.4 GHz when dual-band clients are used.
- Enable 802.11n channel bonding on both 2.4 GHz and 5 GHz to increase the maximum aggregated cell throughput.
Correct answer: BD
Explanation:
Question 8
Company XYZ is redesigning their QoS policy. Some of the applications used by the company are realtime applications. The QoS design must give these applications preference in terms of transmission.
Which QoS strategy can be used to fulfill the requirement?
- weighted fair queuing
- weighted random early detection
- low-latency queuing
- first-in first-out
Correct answer: C
Explanation:
Question 9
As part of workspace digitization, a large enterprise has migrated all their users to Desktop as a Sen/ice (DaaS), by hosting the backend system in their on-premises data center. Some of the branches have started to experience disconnections to the DaaS at periodic intervals, however, local users in the data center and head office do not experience this behavior. Which technology can be used to mitigate this issue?
- tail drop
- traffic shaping
- WRED
- traffic policing
Correct answer: B
Explanation:
Question 10
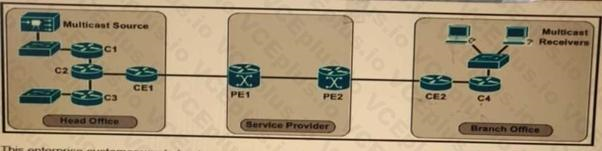
Refer to the exhibit.
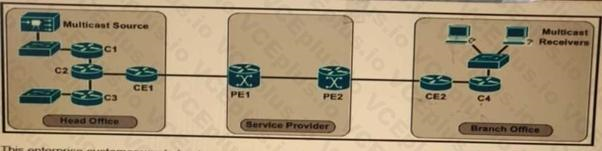
The enterprise customer wants to stream one-way video from their head office to eight branch offices using multicast. Their current service provider provides a Layer3 VPN solution and manages the CE routers, but they do not currently support multicast. Which solution quickly allows this multicast traffic to go through while allowing for future scalability?
- Enable a GRE tunnel between nodes CE1 and CE2
- Enable a GRE tunnel between nodes C2 and C4
- Enable a GRE tunnel between nodes C1 and C4
- Implement hub and spoke MPLS VPN over DMVPN (also known as 2547o DMVPN) between CE1 and CE2
- The service provider must provide a Draft Rosen solution to enable a GRE tunnel between nodes PE1 and PE2
Correct answer: B
Explanation:

