File Info
| Exam | Certified Ethical Hacker v10 Exam |
| Number | 312-50v10 |
| File Name | ECCouncil.312-50v10.TestKing.2019-04-15.177q.vcex |
| Size | 672 KB |
| Posted | Apr 15, 2019 |
| Download | ECCouncil.312-50v10.TestKing.2019-04-15.177q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
An unauthorized individual enters a building following an employee through the employee entrance after the lunch rush. What type of breach has the individual just performed?
- Reverse Social Engineering
- Tailgating
- Piggybacking
- Announced
Correct answer: B
Question 2
Which of the following options represents a conceptual characteristic of an anomaly-based IDS over a signature-based IDS?
- Produces less false positives
- Can identify unknown attacks
- Requires vendor updates for a new threat
- Cannot deal with encrypted network traffic
Correct answer: B
Question 3
You are logged in as a local admin on a Windows 7 system and you need to launch the Computer Management Console from command line.
Which command would you use?
- c:\gpedit
- c:\compmgmt.msc
- c:\ncpa.cp
- c:\services.msc
Correct answer: B
Question 4
_________ is a set of extensions to DNS that provide to DNS clients (resolvers) the origin authentication of DNS data to reduce the threat of DNS poisoning, spoofing, and similar types of attacks.
- DNSSEC
- Resource records
- Resource transfer
- Zone transfer
Correct answer: A
Question 5
PGP, SSL, and IKE are all examples of which type of cryptography?
- Hash Algorithm
- Digest
- Secret Key
- Public Key
Correct answer: D
Question 6
Which of the following scanning method splits the TCP header into several packets and makes it difficult for packet filters to detect the purpose of the packet?
- ICMP Echo scanning
- SYN/FIN scanning using IP fragments
- ACK flag probe scanning
- IPID scanning
Correct answer: B
Question 7
You have successfully gained access to a Linux server and would like to ensure that the succeeding outgoing traffic from this server will not be caught by Network-Based Intrusion Detection Systems (NIDS).
What is the best way to evade the NIDS?
- Out of band signaling
- Protocol Isolation
- Encryption
- Alternate Data Streams
Correct answer: C
Question 8
What is the purpose of a demilitarized zone on a network?
- To scan all traffic coming through the DMZ to the internal network
- To only provide direct access to the nodes within the DMZ and protect the network behind it
- To provide a place to put the honeypot
- To contain the network devices you wish to protect
Correct answer: B
Question 9
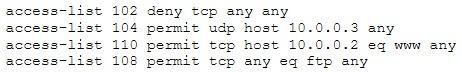
The security administrator of ABC needs to permit Internet traffic in the host 10.0.0.2 and UDP traffic in the host 10.0.0.3. He also needs to permit all FTP traffic to the rest of the network and deny all other traffic. After he applied his ACL configuration in the router, nobody can access to the ftp, and the permitted hosts cannot access the Internet. According to the next configuration, what is happening in the network?
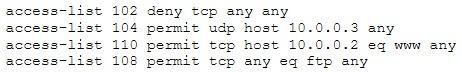
- The ACL 104 needs to be first because is UDP
- The ACL 110 needs to be changed to port 80
- The ACL for FTP must be before the ACL 110
- The first ACL is denying all TCP traffic and the other ACLs are being ignored by the router
Correct answer: D
Question 10
When conducting a penetration test, it is crucial to use all means to get all available information about the target network. One of the ways to do that is by sniffing the network.
Which of the following cannot be performed by the passive network sniffing?
- Identifying operating systems, services, protocols and devices
- Modifying and replaying captured network traffic
- Collecting unencrypted information about usernames and passwords
- Capturing a network traffic for further analysis
Correct answer: B

