File Info
| Exam | IBM WebSphere Message Broker V8.0 System Administration |
| Number | C9530-277 |
| File Name | IBM.C9530-277.PassCertification.2019-02-28.55q.vcex |
| Size | 240 KB |
| Posted | Feb 28, 2019 |
| Download | IBM.C9530-277.PassCertification.2019-02-28.55q.vcex |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
A company has the requirement to have their message flow application running on broker BRK1 communicate with the CICS Transaction Server. The message flow application contains CICSRequest node that has security identity defined as mySecurityIdentity. The CICS Transaction server only accepts the transactions from applications if they are sent by the userId user1 with password password1. Which command does the system administrator need to run to set the userId and password on the broker?
- mqsisetdbparms BRK1 -n SecurityIdentity -u user1 -p password1
- mqsisetdbparms BRK1 -n mySecurityIdentity -u user1 -p password1
- mqsisetdbparms BRK1 -n cics::SecurityIdentity -u user1 -p password1
- mqsisetdbparms BRK1 -n cics::mySecurityIdentity -u user1 -p password1
Correct answer: D
Question 2
A system administrator is configuring Public Key Infrastructure (PKI) for an execution group EG1 that is deployed to broker BRK1. The development team informed the system administrator that their requirement is to send the SOAP requests to an external web service provider. The provider only receives https requests and requires to authenticate the broker requests as well. Which commands does the system administrator need to run to configure PKI at the execution group level?
- mqsichangeproperties BRK1 -e EG1 -o ComIbmJVMManager -n keystoreFile -v keystore.jksmqsichangeproperties BRK1 -e EG1 -o ComIbmJVMManager -n truststoreFile -v truststore.jks
- mqsichangeproperties BRK1 -e EG1 -o ComIbmJVMManager -n keystoreFile -v keystore.jksmqsichangeproperties BRK1 -e EG1 -o HTTPSConnector -n truststoreFile -v truststore.jks
- mqsichangeproperties BRK1 -e EG1 -o ComIbmJVMManager -n keystoreFile -v keystore.jksmqsichangeproperties BRK1 -o BrokerRegistry -n brokerTruststoreFile -v truststore.jks
- mqsichangeproperties BRK1 -o BrokerRegistry -n brokerKeystoreFile -v keystore.jksmqsichangeproperties BRK1 -o BrokerRegistry -n brokerTruststoreFile -v truststore.jks
Correct answer: A
Question 3
A message flow needs to be secured based on the identity credentials. A system administrator is asked to configure the message flow security for authorization, identity mapping and authentication. Which one of the following external security providers can the system administrator use?
- WS-Trust V1.3
- WS-SecurityPolicy V1.2
- IBM Tivoli Federated Identity Manager V6.0
- Lightweight Directory Access Protocol (LDAP) V3
Correct answer: A
Question 4
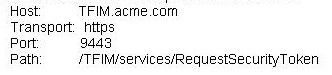
A system administrator has been asked to configure the security profile to the enterprise TFIM v6.2 security server. The profile is to be used by message flows for authentication mapping and authorization from WebSphere Message Broker BRK1.
The TFIM server information provided is as follows:
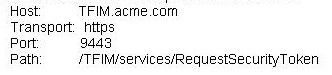
Which command does the system administer need to run to create the profile?
- mqsicreateconfigurableservice BRK1 -c SecurityProfiles -o myTFIMv62Profile-n authentication,mapping,authorization,authenticationConfig,-v "TFIM",TRUE,"TFIM",https://TFIM.acme.com:9443/TFIM/services/RequestSecurityToken
- mqsicreateconfigurableservice BRK1 -c SecurityProfiles -o myTFIMv62Profile-n authentication,mapping,authorization,mappingConfig-v "TFIM v6.2",TRUE,"TFIM v6.2",https://tfim.acme.com:9443/TFIM/services/RequestSecurityToken
- mqsicreateconfigurableservice BRK1 -c SecurityProfiles -o myTFIMv62Profile-n authentication,mapping,authorization,mappingConfig-v "WS-Trust v1.3 STS","WS-Trust v1.3 STS","WS-Trust v1.3 STS",https://tfim.acme.com:9443/TFIM/services/RequestSecurityToken
- mqsicreateconfigurableservice BRK1 -c SecurityProfiles -o myTFIMV62Profile-n authentication,mapping, authorization,configURL-v TRUE, "TFIM", TRUE,https://tfim.acme.com:9443/TFIM/services/RequestSecurityToken
Correct answer: C
Question 5
A development team has been notified that all the requests serviced by their SOAPInput node message flow will now contain wsse headers for authentication, encryption and signatures. The system administrator created the security profile with authentication set to use LDAP and asked the development team to associate the flow's BAR file with the security profile and redeploy it to the broker. When the requests were sent to the broker, they were not processed. What did the system administrator miss?
The system administrator missed: 1. creating the policy set
- 2. creating the consumer policy set binding3. putting key information in the policy set4. adding the private keys to the keystore5. pointing the broker to it and giving the names of the policy set and the policy set binding to the developers for associating them with the BAR file before the redeploy
- 2. creating the provider policy set binding3. putting the key information in the policy set binding4. adding the private keys only to the keystore5. pointing the broker to it and giving the names of the policy set and the policy set binding to the developers for associating them with the BAR file before the redeploy
- 2. creating the consumer policy set binding3. putting the key information in the policy set4. adding the private and public keys to the keystore and truststore5. pointing the broker to them and giving the names of the policy set and the policy set binding to the developers for associating them with the BAR file before the redeploy
- 2. creating the provider policy set binding3. putting the key information in the policy set binding4. adding the private and public keys to the keystore and truststore5. pointing the broker to them and giving the names of the policy set and the policy set binding to the developers for associating them with the BAR file before the redeploy
Correct answer: D
Question 6
A system administrator is asked to assist a developer who has setup a message flow that uses an HTTP Input node to securely process SOAP messages deployed to run on LINUX broker BRK1. After xdeploying the flow into the production environment, the application invoking the flow is receiving a failure response. What should the system administrator do to get the developer to understand the security exception? Have the developer:
- change the validation property to Content and Value.
- change the identity token type on HTTP Input node to Username.
- change the Fault format property of the HTTP Input Node to SOAP1.2 and retest the failing request.
- set Treat Security Exceptions as normal exceptions property of the HTTP Input Node, redeploy the message flow and retest failing request.
Correct answer: D
Question 7
A system administrator configures a message flow security to perform the end-to-end processing of all identity credentials that are carried in a message through a message flow using IBM Tivoli Federated Identity Manager (TFIM). Which of the following three tasks performed by the security manager require the use of TFIM? (Choose three.)
- Authenticate the identity.
- Enable default propagation.
- Map the identity to an alternative identity.
- Extract the identity from an inbound message.
- Propagate either the alternative identity or the original identity with an outbound message.
- Check that either the alternative identity or the original identity is authorized to access the message flow.
Correct answer: ACF
Question 8
The broker administration security has been set up on a broker BRK1 for a developer dev1. In addition to the existing security setting, a system administrator is asked to set security permissions for data capture so that the developer can perform the record and replay actions on the broker. Which command does the system administrator need to run?
- setmqaut -m BRK1 -n "SYSTEM.BROKER.DC.AUTH " -t q -p dev1 +inq +put +set
- setmqaut -m BRK1 -n "SYSTEM.BROKER.DC.AUTH " -t q -p dev1 -all +inq +put
- setmqaut -m BRK1 -n "SYSTEM.BROKER.AUTH.** " -t q -p dev1 +inq +put +set +get
- setmqaut -m BRK1 -n "SYSTEM.BROKER.AUTH.** " -t q -p dev1 -all +inq +put +set +get
Correct answer: A
Question 9
A system administrator was asked to create a security identity associated "ftp::FTP1" with a user ftpuser1 and its password password1. The message flow containing the FileOutput node with the correct ftp credentials has been deployed to the broker BRK1 on Linux system already. The system administrator ran the command: mqsisetdbparms BRK1 -n ftp::FTP1 -u ftp\user1 -p password1. When the transaction was processed, the output file was not generated on the ftp server and the failure reported incorrect user credentials.
What did the system administrator do wrong?
- Supplied incorrect userId and password in the command.
- Used the incorrect format of security identity in the command.
- Added the extra escape character with -u option in the command.
- Did not add an extra escape character with -u option in the command.
Correct answer: D
Question 10
A company has multiple users that access broker using web user interface. The system administrator of the company has been asked to define security for a group of users in such a way that user1 is able to view all the broker resources, user2 is able to view and modify all the broker resources and user3 is able to view and modify selected broker resources.
What does the system administrator need to do?
- Only run the command mqsiwebuseradmin
- Only ensure that broker administration security is active.
- Define security and roles at the Operating system level.
- Ensure broker administration security is active and run the command mqsiwebuseradmin
Correct answer: D

