File Info
| Exam | MuleSoft Certified Developer - Level 2 (Mule 4) |
| Number | MCD-Level-2 |
| File Name | Mulesoft.MCD-Level-2.ExamDumps.2024-06-17.29q.tqb |
| Size | 3 MB |
| Posted | Jun 17, 2024 |
| Download | Mulesoft.MCD-Level-2.ExamDumps.2024-06-17.29q.tqb |
How to open VCEX & EXAM Files?
Files with VCEX & EXAM extensions can be opened by ProfExam Simulator.
Coupon: MASTEREXAM
With discount: 20%





Demo Questions
Question 1
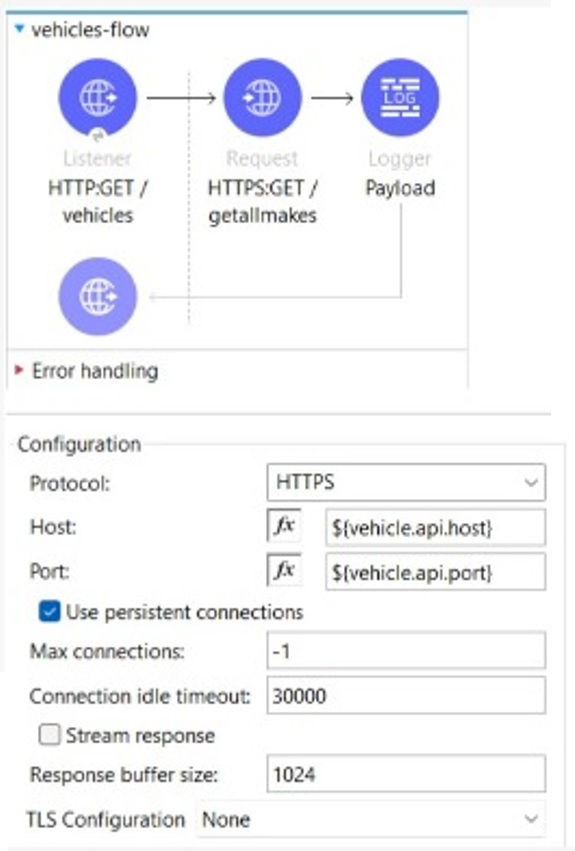
The flow is invoicing a target API. The API's protocol is HTTPS. The TLS configuration in the HTTP Request Configuration global element is set to None. A web client submits a request to http:localhost:8081/vehicles.
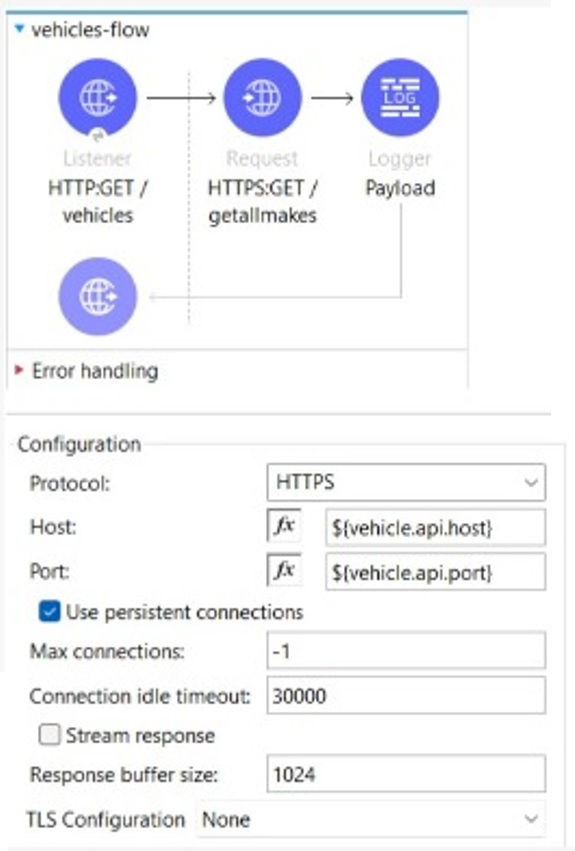
If the certificate of the target API is signed by a certificate authority (CA), what is true about the HTTP Request operation when the flow executes?
- The HTTP Request operation will succeed if the CA'S certificate is present in the JRE's default keystore
- The HTTP Request operation will succeed if the CA's certificate is present in the JRE's default truststore.
- The HTTP Request operation will always succeed regardless of the CA
- The HTTP Request operation will always fail regardless of the CA
Correct answer: B
Explanation:
The HTTP Request operation will use the default truststore of the JRE to validate the certificate of the target API. If the CA's certificate is present in the truststore, the operation will succeed. Otherwise, it will fail with a handshake exception.Reference: https://docs.mulesoft.com/mule-runtime/4.3/tls-configuration#tls-default The HTTP Request operation will use the default truststore of the JRE to validate the certificate of the target API. If the CA's certificate is present in the truststore, the operation will succeed. Otherwise, it will fail with a handshake exception.
Reference: https://docs.mulesoft.com/mule-runtime/4.3/tls-configuration#tls-default
Question 2
When a client and server are exchanging messages during the mTLS handshake, what is being agreed on during the cipher suite exchange?
- A protocol
- The TLS version
- An encryption algorithm
- The Public key format
Correct answer: C
Explanation:
A cipher suite is a set of cryptographic algorithms that are used to secure the communication between a client and a server. A cipher suite consists of four components: a key exchange algorithm, an authentication algorithm, an encryption algorithm, and a message authentication code (MAC) algorithm. During the cipher suite exchange, the client and the server agree on which encryption algorithm to use for encrypting and decrypting the data.Reference: https://docs.mulesoft.com/mule-runtime/4.3/tls-configuration#cipher-suites A cipher suite is a set of cryptographic algorithms that are used to secure the communication between a client and a server. A cipher suite consists of four components: a key exchange algorithm, an authentication algorithm, an encryption algorithm, and a message authentication code (MAC) algorithm. During the cipher suite exchange, the client and the server agree on which encryption algorithm to use for encrypting and decrypting the data.
Reference: https://docs.mulesoft.com/mule-runtime/4.3/tls-configuration#cipher-suites
Question 3
A healthcare portal needs to validate the token that it sends to a Mule API. The developer plans to implement a custom policy using the HTTP Policy Transform Extension to match the token received in the header from the heathcare portal.
Which files does the developer need to create in order to package the custom policy?
- Deployable ZIP file, YAML configuration file
- JSON properties file, YAML configuration file
- JSON properties file, XML template file
- XML template file, YAML configuration file
Correct answer: D
Explanation:
To package a custom policy using the HTTP Policy Transform Extension, the developer needs to create an XML template file and a YAML configuration file. The XML template file defines the policy logic using Mule components and placeholders for user-defined properties. The YAML configuration file defines the metadata of the policy, such as its name, description, category, parameters, and dependencies.Reference: https://docs.mulesoft.com/api-manager/2.x/http-policy-transform#packaging-the-policy To package a custom policy using the HTTP Policy Transform Extension, the developer needs to create an XML template file and a YAML configuration file. The XML template file defines the policy logic using Mule components and placeholders for user-defined properties. The YAML configuration file defines the metadata of the policy, such as its name, description, category, parameters, and dependencies.
Reference: https://docs.mulesoft.com/api-manager/2.x/http-policy-transform#packaging-the-policy


